The platform used for the file system produced: fl2440 (ARM9)
The cross-section of a barley root
Ranunculus Root Cross Section
Large, mature tree roots above the soil
Wikimedia Commons has media related to .
Wikiquote has quotations related to Root.
- Botany – University of Arkansas at Little Rock
- Time-lapse photography of root growth on YouTube
This article is about the part of a plant. For other uses, see Root (disambiguation).
«Rooted» redirects here. For the 1969 play and TV movie adaptation, see Rooted (film). For the song, see Ciara discography.

Primary and secondary roots in a cotton plant
A true root system consists of a primary root and secondary roots (or lateral roots).
- Three Main Types
- Evolution Made Trees Opportunistic
- Content: Root System in Plants
- Types of Root
- Characteristics
- Parts of Root
- Five Functions of Root
- Introduction to Embedded Linux File System
- 1. Basic concepts:
- 2. Common file system:
- FLASH-based file system:
- Disadvantages of Tree Data Structure
- Properties of Tree Data Structure
- Seven, install busybox
- Types of Tree data structures
- What is the degree of a node in a tree?
- Orders of Root
- Primary Roots
- Secondary Roots
- Tertiary Roots
- Representation of Tree Data Structure
- Representation of a Node in Tree Data Structure:
- Example of Tree data structure
- Differences between Monocot and Dicot roots
- Fourth, create a symbolic link file in the Var directory
- Basic Operation Of Tree Data Structure
- Advantages of Tree Data Structure
- C++
- What is the depth of the tree?
- Functions of Roots
- What is a height of a tree?
- Shade avoidance response
- Structure of Roots
- Root Cap
- Region of Meristematic Activity
- Region of Elongation
- Region of Maturation
- Javascript
- Root system architecture (RSA)
- Terms and components
- What is a child node?
- Python3
- What is a root node?
- Characteristics of Root
- Application of Tree Data Structure
- Process summary
- Related operations in etc directory
- 1. Create the /etc/inittab file
- 2. Create etc/init.d/rcS script
- 3. Configure the network card self-start script:
- 4. Create a startup script that supports the /apps/etc directory
- 5. Modify all file permissions in the init.d directory
- 6. Create fstab file
- 7. Create hostname, hosts, TZ files
- 8. Create a profile file
- 9. Create a port number file protocols used by some protocols
- 10. Create mdev.conf file
- 11. Create user group group file
- 12. Create a user passwd file:
- 13. Create a password mapping shadow file
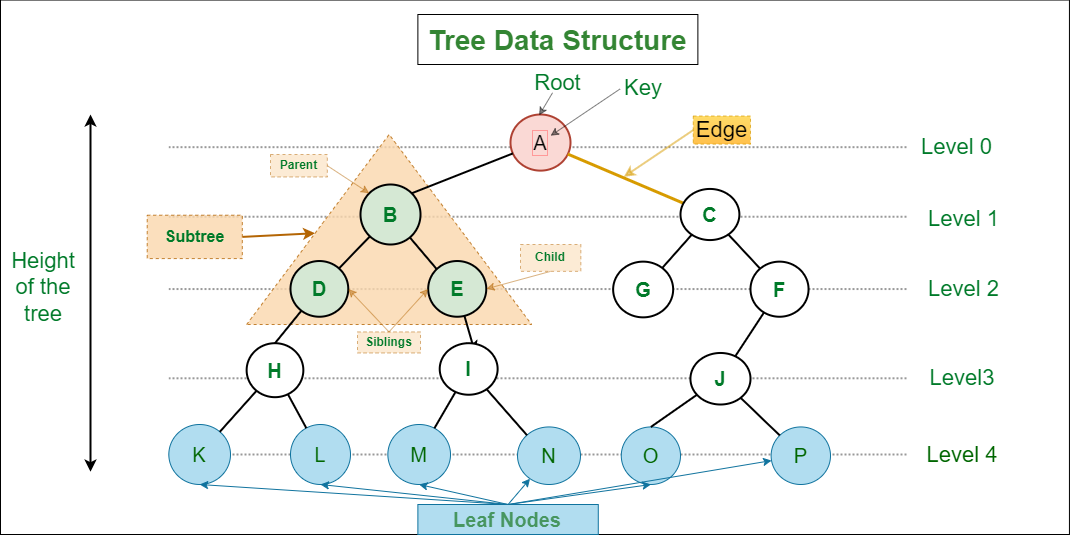
- Basic Terminologies In Tree Data Structure
- Java
- What is root?
- Importance of root node
- Modification of Root
- Modification for Food capacity
- Modification for Support
- Modified for Respiratory
- FAQs on Root
- Five, copy the dynamic library in the cross compiler to the corresponding directory
- Two, create a directory
- 3. Create a device file in the Dev directory
- Need for Tree Data Structure
- What is a parent node?
- Eight, transplant dropbear
- 1. First compile and generate the PC version, which is used when making the key
- 2. Compile the ARM version
- 3. Create a startup script in the file system
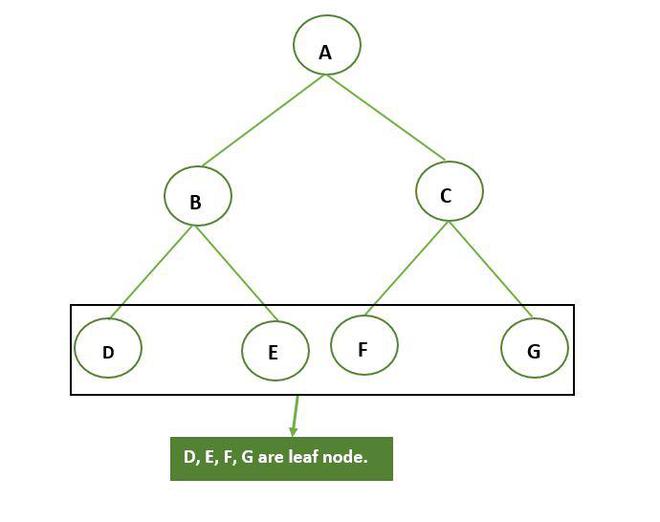
- What is a leaf node?
- Why Tree is considered a non-linear data structure?
Stilt roots of Maize plant
Cross section of an adventitous crown root of pearl millet (Pennisetum glaucum)
Roots forming above ground on a cutting of an Odontonema («Firespike»)
The growing tip of a fine root
Trees are nonlinear data structures that organize data hierarchically and in a recursive manner.
It is a method of organizing and storing data in the computer in a way that makes it more effective to use. Nodes in the graph are connected via edges. It has different types of nodes which are called parent node, child node, leaf node, etc.
A root is a piece of a vascular plant typically present under the ground. Its essential functions include jetty of the plant, ingestion of water and disintegrated minerals and conduction of these to the stem, and capacity to hold food varieties. The root contrasts from the stem principally by lacking leaf scars and buds, having a root cap, and having branches that start from inner tissue as opposed to from buds.
Growth from apical meristems is known as primary growth, which encompasses all elongation.
Secondary growth encompasses all growth in diameter, a major component of woody plant tissues and many nonwoody plants. For example, storage roots of sweet potato have secondary growth but are not woody. Secondary growth occurs at the lateral meristems, namely the vascular cambium and cork cambium. The former forms secondary xylem and secondary phloem, while the latter forms the periderm.
Tree roots at Port Jackson
Fluorescent imaging of an emerging lateral root.
A tree data structure is a hierarchical structure that is used to represent and organize data in a way that is easy to navigate and search. It is a collection of nodes that are connected by edges and has a hierarchical relationship between the nodes.
The topmost node of the tree is called the root, and the nodes below it are called the child nodes. Each node can have multiple child nodes, and these child nodes can also have their own child nodes, forming a recursive structure.
This data structure is a specialized method to organize and store data in the computer to be used more effectively. It consists of a central node, structural nodes, and sub-nodes, which are connected via edges. We can also say that tree data structure has roots, branches, and leaves connected with one another.
Introduction to Tree – Data Structure and Algorithm Tutorials
Cross section of a mango tree
The distribution of vascular plant roots within soil depends on plant form, the spatial and temporal availability of water and nutrients, and the physical properties of the soil. The deepest roots are generally found in deserts and temperate coniferous forests; the shallowest in tundra, boreal forest and temperate grasslands. The deepest observed living root, at least 60 metres below the ground surface, was observed during the excavation of an open-pit mine in Arizona, USA. Some roots can grow as deep as the tree is high. The majority of roots on most plants are however found relatively close to the surface where nutrient availability and aeration are more favourable for growth. Rooting depth may be physically restricted by rock or compacted soil close below the surface, or by anaerobic soil conditions.
- Baldocchi DD, Xu L (October 2007). «What limits evaporation from Mediterranean oak woodlands–The supply of moisture in the soil, physiological control by plants or the demand by the atmosphere?». Advances in Water Resources. 30 (10): 2113–22. Bibcode:2007AdWR…30.2113B. doi:10.1016/j.advwatres.2006.06.013.
- Brundrett, M. C. (2002). «Coevolution of roots and mycorrhizas of land plants». New Phytologist. 154 (2): 275–304. doi:. PMID 33873429.
- Clark L (2004). «Primary Root Structure and Development – lecture notes» . Archived from the original on 3 January 2006.
- Coutts MP (1987). «Developmental processes in tree root systems». Canadian Journal of Forest Research. 17 (8): 761–767. doi:10.1139/x87-122.
- Raven JA, Edwards D (2001). «Roots: evolutionary origins and biogeochemical significance». Journal of Experimental Botany. 52 (Suppl 1): 381–401. doi:10.1093/jxb/52.suppl_1.381. PMID 11326045.
- Schenk HJ, Jackson RB (2002). «The global biogeography of roots». Ecological Monographs. 72 (3): 311–328. doi:10.2307/3100092. JSTOR 3100092.
- Sutton RF, Tinus RW (1983). «Root and root system terminology». Forest Science Monograph. 24: 137.
- Phillips WS (1963). «Depth of roots in soil». Ecology. 44 (2): 424. doi:10.2307/1932198. JSTOR 1932198.
- Caldwell MM, Dawson TE, Richards JH (1998). «Hydraulic lift: consequences of water efflux from the roots of plants». Oecologia. 113 (2): 151–161. Bibcode:1998Oecol.113..151C. doi:10.1007/s004420050363. PMID 28308192. S2CID 24181646.
Roots can also protect the environment by holding the soil to reduce soil erosion
The term root crops refers to any edible underground plant structure, but many root crops are actually stems, such as potato tubers. Edible roots include cassava, sweet potato, beet, carrot, rutabaga, turnip, parsnip, radish, yam and horseradish. Spices obtained from roots include sassafras, angelica, sarsaparilla and licorice.
Sugar beet is an important source of sugar. Yam roots are a source of estrogen compounds used in birth control pills. The fish poison and insecticide rotenone is obtained from roots of Lonchocarpus spp. Important medicines from roots are ginseng, aconite, ipecac, gentian and reserpine. Several legumes that have nitrogen-fixing root nodules are used as green manure crops, which provide nitrogen fertilizer for other crops when plowed under. Specialized bald cypress roots, termed knees, are sold as souvenirs, lamp bases and carved into folk art. Native Americans used the flexible roots of white spruce for basketry.
Trees stabilize soil on a slope prone to landslides. The root hairs work as an anchor on the soil.
Vegetative propagation of plants via cuttings depends on adventitious root formation. Hundreds of millions of plants are propagated via cuttings annually including chrysanthemum, poinsettia, carnation, ornamental shrubs and many houseplants.
Roots can also protect the environment by holding the soil to reduce soil erosion. This is especially important in areas such as sand dunes.
From my previous post on roots, we know that tree roots provide structural support, and they are the conduit for nutrient absorbsion. Trees have to have healthy root systems to support the trunk and canopy. Tree root systems are loosely classified by their growing patterns. These patterns are most obvious in young trees and trees growing in optimal environments.
Three Main Types
Tap root systems are characterized by one central root extending down from the main trunk. Usually oaks, hickory, and walnut trees fall into this category. This root structure is more obvious in young trees. Looking at the way the trunk of this very large walnut tree goes straight down into the ground suggests that the roots may extend down more than laterally. By looking at the size of this tree, it is probably located in an area for optimal growth and root structure.
Heart root systems have multiple primary roots that extend laterally from the trunk and are attached to numerous secondary roots. These are mostly horizontal in their growing pattern. Some trees that characteristically have this type of root system are red oak, honey locust, basswood, sycamore, and pines. This is a picture of three pine trees and it shows how the trunk flares at the base suggesting that there are primary and lateral roots.
Flat root systems don’t have the obvious primary roots. They are horizontal and spread laterally. Trees that characteristically have this type of root system are birch, fir, spruce, sugar maple, cottonwood, silver maple, hackberry. This is a picture of a sugar maple tree. I am guessing that for years the mulch covered the roots. These roots are tangled and not extending straight from the trunk which would be more optimally characteristic of a flat root system.
Evolution Made Trees Opportunistic
Trees are opportunistic and the root systems adapt to the soils conditions, physical barriers, and weather. As trees mature, their typical root system may or may not be evident. This is a great example of beech tree root systems in the forest. Young seedling beech trees typically have a tap root system. When these trees grow in the woods where there is a large humus accumulation (decay), as they mature, that root system changes to roots that extend laterally and colonize in the highly organic upper layers of the soil.


This tree is located on a very rocky hillside in West Virginia. As you can see, years ago the roots extended over rocks to try to reach viable soil.
The root system remains subterranean or underground the soil in the case of vascular plants. Therefore, it provides strength and rigidity to the growing shoot system against adverse conditions.
Some of the trees (like a banyan tree, bonsai tree etc.) have their root system over the ground that refers to aerial roots. Unlike stems, roots are irregularly branched structures that lack nodes and internodes.
Plants like mosses and liverworts lack the presence of the root system. Cellular processes like photosynthesis help in the functioning and metabolism of the root system. A root system lacks stomata that are present in leaves and stems.
The root system consists of a thimble-like root cap and thread-like root hairs. In this context, we will learn the definition, types, characteristics, parts and functions of the root system in plants.
Content: Root System in Plants
The root system refers to the ramose structures that exist subterranean or superterranean to the earth surface. A root consists of the hard root cap, primary root meristem and root hairs. The growth of the root system depends upon the soil composition, soil type, type of plant species and growth conditions. Roots are complex structures whose total dry weight may exceed the total weight of the plant body. A seed first develops a radicle or primary root and later forms secondary, tertiary etc., roots.
Types of Root
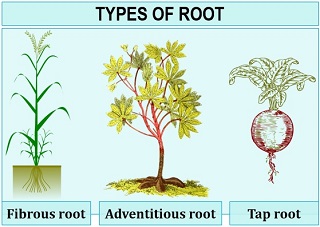
- Taproot system: A taproot is a primary root system consisting of lateral branched roots with fine rootlets.
Example: Carrot, turnip etc. - Fibrous root system: It appears as a large and equal-sized root, which originates from the base of the stem by replacing a primary root. Fibrous roots possess a bushy appearance and consist of thin root fibres.
Example: Wheat, rice, maize grass etc. - Adventitious root system: In this type, massive root growth occurs from any part of the plant body other than the primary root.
Example: Banyan, Monstera etc.
Characteristics
- Roots are mostly subterranean to the plant axis.
- A root system is:
- Positively geotropic.
- Negatively phototropic
- Positively hydrotropic.
- Root comprises unicellular structures or root hairs that absorb water from the soil.
- The cuticle or waxy coating that surrounds the leaf epidermis is absent in the root system.
- The root system lacks chlorophyll and stomata.
- Unlike stems, it does not have nodes and internodes.
- Sometimes, a root undergoes structural modification to perform functions like storage, respiration, physical support etc.
Parts of Root
A structure of root generally comprises of three parts:
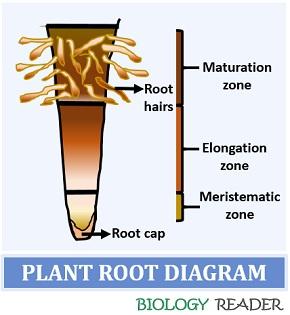
Root cap: It is found at the tip of the root system and has a thimble-like appearance. Root-cap is a multicellular structure present proximal to the primary meristem. It also secretes mucilage that acts as a lubricating agent. A mucilage secreted by the root cap protects the root system against dryness. Few aquatic plants like Pistia, Ecchornia etc., have a root pocket instead of a root cap.
Root meristem: It is found 1 mm above the root cap and refers to the “Zone of meristematic activity”. This region contains cells of small size, thin-walled and dense protoplasm. Here, the cells undergo repeated cell divisions. The “Zone of elongation” refers to the region where some cells enlarge rapidly, located proximal to the meristematic zone. The cells in the elongation zone extend the root length.
Root hairs: The cells in the zone of elongation undergo multiplication and differentiation to develop mature cells. The mature cells proximal to the area of elongation constitute a region of maturation. The epidermal cells of the maturation zone give rise to the fine, thread-like root hairs. Root hairs perform a functional role in water and mineral absorption from the soil.
Five Functions of Root
Roots perform five distinct roles in plants:
Anchorage and Physical support: A root system anchors the plant body or the shoot system to the soil. Roots under the ground help in maintaining the plant’s posture by giving physical support. Taproots provide better attachment of the plant to the soil and make a plant resistant to toppling during storms.
Absorption and Conduction: Roots promote absorption of water and conduction of dissolved minerals and nutrients in the soil to the plant body. Root hairs are fine structures existing in close vicinity to the ground and absorb nutrients from the soil.
The root hairs uptake the nutrients and conduct them to the shoot system via xylem through capillary action. Therefore, the root system provides nourishment to the plant for growth or development. In addition, fibrous roots are more efficient in absorbing nutrients deep inside the soil.
Food Storage: The root system also acts as a storage organ of the plant, which mainly stores water and carbohydrates. The plant prepares its food during photosynthesis and stores in the specialized part of the plant like leaf, stem and roots. Taproots are more effective in food absorption than fibrous roots.
Role in Photosynthesis: Roots play an essential role in the process of photosynthesis. A plant gets water from the root system and releases excessive water through stomata through transpiration. As the water vapours release out of the stomata, CO2 enters the plant cell necessary for photosynthesis.
Ecological functions: Roots are part of soil ecology, promoting soil aggregation and protecting a plant from being carried away by wind or water.
Introduction to Embedded Linux File System
1. Basic concepts:
Linux supports a variety of file systems, including ext2, ext3, vfat, ntfs, iso9660, jffs, romfs, and nfs. In order to manage various file systems in a unified manner, Linux has introduced the virtual file system VFS (Virtual File System) for each The class file system provides a unified operation interface and application programming interface. When Linux starts, the first thing that must be mounted is the root file system; if the system cannot mount the root file system from the specified device, the system will make an error and exit the startup. You can then mount other file systems automatically or manually. Therefore, different file systems can exist in a system at the same time.
Different file system types have different characteristics, so there are different applications according to the hardware characteristics of the storage device, system requirements, etc. In embedded Linux applications, the main storage devices are RAM (DRAM, SDRAM) and ROM (usually FLASH memory). Commonly used storage device-based file system types include: jffs2, yaffs, cramfs, romfs, ramdisk, ramfs/ tmpfs etc.

2. Common file system:
(1)initramfs
initramfs is compiled while compiling the kernel and generates an image file with the kernel. It can be compressed or uncompressed, but currently only supports the cpio package format. It is a very simple way to make and make the root file system. You can also boot the real file system by executing the program in this file system, so that the job of loading the root file system is not the job of the kernel, but the job of initramfs . Because initramfs uses the cpio package format, it is easy to compile and link a single file, directory, and node to the system. This is very convenient to use in a very simple system, and there is no need to mount a file system separately.
But because the cpio package is actually a description language package for files, directories, and nodes, in order to describe a file, directory, and node, a lot of extra description text overhead must be added, especially for directories and nodes , Itself is very small and adds a lot of additional description text, which makes the cpio package much larger than the corresponding image file.
(2)Ramdisk
ramdisk is a memory-based virtual file system (not an actual file system). It treats a part of the fixed size (this size is configured when compiling the kernel’s make menuconfig) as the memory One partition of the hard disk is used. Ramdisk is a mechanism to load the actual file system into memory, and can be used as the root file system, usually we use ext2 or ext3 file system to format it. Because the ramdisk operates in the memory, we can add, modify, delete, etc. the files inside, but once the power is off, there is nothing. Due to this feature, we can put some frequently accessed but not changed files (such as read-only root file system) in the memory through Ramdisk, which can significantly improve the performance of the system.
In the boot phase of Linux, both the kernel and ramdisk are loaded by the bootloader to the specified location of the memory () at boot time, and initrd provides a mechanism to transfer the kernel image and root file The system loads into memory together. initrd is the boot loader initialized RAM disk. As the name implies, it is a ramdisk used when the system is initialized and booted. Its function is to improve the kernel module mechanism and make the kernel initialization process more flexible.
(3) ramfs/tmpfs
Ramfs is a memory-based file system developed by Linus Torvalds. It works at the virtual file system (VFS) layer. It cannot be formatted. You can create multiple ones. You can specify the maximum value when creating it. The amount of memory that can be used. (Actually, VFS can be regarded as a kind of memory file system in essence, which unifies the representation of files in the kernel and buffers the disk file system.) Ramfs/tmpfs file system puts all files in RAM, Therefore, read/write operations occur in RAM, and ramfs/tmpfs can be used to store some temporary or frequently modified data, such as /tmp and /var directories, which not only avoids the loss of reading and writing to Flash memory, but also improves Data read and write speed. The main difference between Ramfs/tmpfs and traditional Ramdisk is that it cannot be formatted, and the file system size can vary with the size of the file content. But none of them can be used as a root file system like a ramdisk, but can only be used as a pseudo file system like procfs and devfs.
(5) Pseudo file system
The above discussion is based on storage device file system (memory-based file system), they can be used as Linux root file system (except tmpfs and ramfs). In fact, Linux also supports logical or pseudo file systems, such as procfs (proc file system) for obtaining system information, and devfs (device file system) and sysfs for maintaining device files.
FLASH-based file system:
1、 jffs2
JFFS file system was originally developed by Sweden Axis Communications based on the Linux2.0 kernel for embedded systems. JFFS2 (Journalling Flash File System v2, journal flash file system version 2) is a flash file system developed by RedHat based on JFFS. It was originally an embedded file system developed for RedHat’s embedded product eCos. JFFS2 can also be used in Linux, uCLinux. It is mainly used for NOR flash memory, based on the MTD driver layer, and features: readable and writable, data compression-supported, hash table-based log file system, and crash/power-down safety protection, providing «write balance» «Support and so on. The main disadvantage is that when the file system is full or close to full, the running speed of jffs2 is greatly slowed down due to garbage collection.
Jffs2 is not suitable for NAND flash memory mainly because the capacity of NAND flash memory is generally large, which causes the memory space occupied by jffs2 to maintain log nodes to increase rapidly. In addition, the jffs2 file system is When mounting, it is necessary to scan the entire FLASH content to find all log nodes and establish a file structure, which consumes a lot of time for large-capacity NAND flash memory.
Currently jffs3 is under development. For detailed documentation on the use of the jffs2 series of file systems, please refer to mtd-jffs-HOWTO.txt in the MTD patch package.
5、 Romfs
The traditional Romfs file system is a simple, compact, and read-only file system. It does not support dynamic erasing and saving. Data is stored in order. Therefore, it supports applications using XIP( eXecute In Place (on-chip running) mode runs, saving RAM space when the system is running. The uClinux system usually uses the Romfs file system.
6. Other file systems
fat/fat32 can also be used for the extended memory of actual embedded systems (such as SD cards for PDAs, Smartphones, digital cameras, etc.), mainly for better compatibility with the most popular Windows desktop The operating system is compatible. ext2 can also be used as an embedded Linux file system, but using it for FLASH flash memory will have many disadvantages.
Disadvantages of Tree Data Structure
- Unbalanced Trees, meaning that the height of the tree is skewed towards one side, which can lead to inefficient search times.
- Trees demand more memory space requirements than some other data structures like arrays and linked lists, especially if the tree is very large.
- The implementation and manipulation of trees can be complex and require a good understanding of the algorithms.
Properties of Tree Data Structure
- Number of edges: An edge can be defined as the connection between two nodes. If a tree has N nodes then it will have (N-1) edges. There is only one path from each node to any other node of the tree.
- Depth of a node: The depth of a node is defined as the length of the path from the root to that node. Each edge adds 1 unit of length to the path. So, it can also be defined as the number of edges in the path from the root of the tree to the node.
- Height of a node: The height of a node can be defined as the length of the longest path from the node to a leaf node of the tree.
- Height of the Tree: The height of a tree is the length of the longest path from the root of the tree to a leaf node of the tree.
- Degree of a Node: The total count of subtrees attached to that node is called the degree of the node. The degree of a leaf node must be 0. The degree of a tree is the maximum degree of a node among all the nodes in the tree.
Seven, install busybox
[yangni busybox-.]vim #Modify CROSS_COMPILER to (change to cross compiler): ?= -/arm920t/usr/bin/arm-linux- Busybox Settings General Configuration [*] Don't use /usr Installation Options ( behavior) What kind applet links install ( soft-links) (/opt/rootfs) BusyBox installation prefix#Here path/opt/rootfs is the path of the root file system we made#Other options combined with your own needs customization: ELF 32-bit LSB executable, ARM, version 1 (SYSV), statically linked, strippedYou will probably need to make your busybox binary
setuid root to ensure all configured applets willAfter the installation is successful, the linuxrc file appears in the rootfs directory:
Linuxrc rebuilds the file allocation table inittab; then executes the system initialization process /sbin/init. /mnt/etc/init.d/rcS complete the mount of each file system
Types of Tree data structures
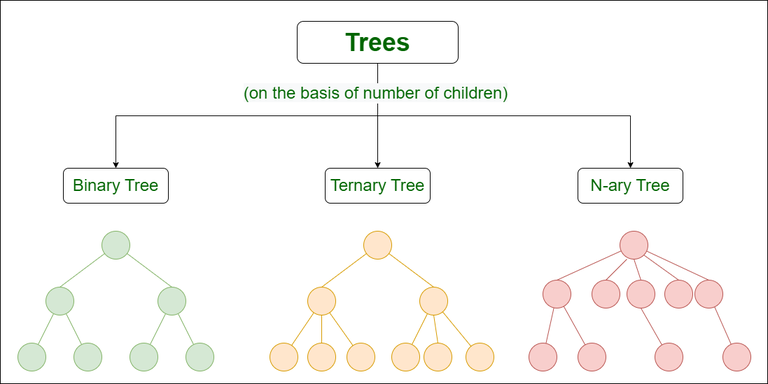
- Binary tree: In a binary tree, each node can have a maximum of two children linked to it. Some common types of binary trees include full binary trees, complete binary trees, balanced binary trees, and degenerate or pathological binary trees.
- Ternary Tree: A Ternary Tree is a tree data structure in which each node has at most three child nodes, usually distinguished as “left”, “mid” and “right”.
- N-ary Tree or Generic Tree: Generic trees are a collection of nodes where each node is a data structure that consists of records and a list of references to its children(duplicate references are not allowed). Unlike the linked list, each node stores the address of multiple nodes.
What is the degree of a node in a tree?
The Degree of a node in the tree is the summation of the number of child nodes connected to it, and the node which has the highest number of child nodes in a tree is also known as the Degree of a tree.
Degree of tree
Orders of Root
Primary Roots
The roots grow directly from the radicle. It is the most important part of the root present in the center. The tap root system is from the primary roots.
Secondary Roots
Lateral roots are the other name for secondary roots. Primary roots give rise to secondary roots.
Tertiary Roots
The tertiary root is raised from the secondary roots. Some of the roots lost the geotropism. The tips of the roots have some root hairs which are covered with root caps.
Representation of Tree Data Structure

Representation of Tree Data Structure
Representation of a Node in Tree Data Structure:
Example of Tree data structure

- Node 1 is the root node
- 1 is the parent of 2 and 3
- 2 and 3 are the siblings
- 4, 5, 6, and 7 are the leaf nodes
- 1 and 2 are the ancestors of 5
Differences between Monocot and Dicot roots
Fourth, create a symbolic link file in the Var directory
[yanngi rootfs]$ ln -s /tmp /lock
[yanngi rootfs]$ ln -s /tmp /log
[yanngi rootfs]$ ln -s /tmp /run
[yanngi rootfs]$ ln -s /tmp /tmp
[yanngi rootfs]$ ls -l /
total
lrwxrwxrwx yangni trainning Apr : lock /tmp
lrwxrwxrwx yangni trainning Apr : log /tmp
lrwxrwxrwx yangni trainning Apr : run /tmp
lrwxrwxrwx yangni trainning Apr : tmp /tmpBasic Operation Of Tree Data Structure
- Create – create a tree in the data structure.
- Insert − Inserts data in a tree.
- Search − Searches specific data in a tree to check whether it is present or not.
- Traversal:
- Preorder Traversal – perform Traveling a tree in a pre-order manner in the data structure.
- In order Traversal – perform Traveling a tree in an in-order manner.
- Post-order Traversal –perform Traveling a tree in a post-order manner.
Advantages of Tree Data Structure
- Tree offer Efficient Searching Depending on the type of tree, with average search times of O(log n) for balanced trees like AVL.
- Trees provide a hierarchical representation of data, making it easy to organize and navigate large amounts of information.
- The recursive nature of trees makes them easy to traverse and manipulate using recursive algorithms.
C++
using namespace std;
void addEdge(int x, int y, vector<vector<int> >& adj)
void printParents(int node, vector<vector<int> >& adj,
if (parent == 0)
cout << node << "->Root" << endl;
cout << node << "->" << parent << endl;
if (cur != parent)
printParents(cur, adj, node);
void printChildren(int Root, vector<vector<int> >& adj)
int node = q.front();
cout << node << "-> ";
cout << cur << " ";
cout << endl;
void printLeafNodes(int Root, vector<vector<int> >& adj)
for (int i = 1; i < adj.size(); i++)
cout << i << " ";
cout << endl;
void printDegrees(int Root, vector<vector<int> >& adj)
cout << i << ": ";
if (i == Root)
int N = 7, Root = 1;
vector<vector<int> > adj(N + 1, vector<int>());
addEdge(1, 2, adj);
addEdge(1, 3, adj);
addEdge(1, 4, adj);
addEdge(2, 5, adj);
addEdge(2, 6, adj);
addEdge(4, 7, adj);
cout << "The parents of each node are:" << endl;
printParents(Root, adj, 0);
cout << "The children of each node are:" << endl;
cout << "The leaf nodes of the tree are:" << endl;
cout << "The degrees of each node are:" << endl;
What is the depth of the tree?
At the root node, the depth is minimum and at the leaf node, it is maximum. In the example given below at root node (A), it is 0 and at leaf node (F) it is maximum which is 2.
Example of depth of tree
Let’s take one more example to clarify the concept.
Here you can notice that the depth of node (C) is zero as it is a leaf node.
Functions of Roots
Roots fill different roles that are essential for the endurance of the plants. They are a vital or incorporated framework that helps the plant in:
- Anchoring: Roots are the explanation plants stay connected to the ground. They support the plant body, guaranteeing that it stands erect.
- Absorption: Primary function of the roots is to assimilate water and break down minerals from the dirt. This is urgent as it helps during the time spent in photosynthesis.
- Storage: Plants get produce food through photosynthesis and save it as starch in the leaves, shoots, and roots. Conspicuous models incorporate carrots, radish, beetroot, and so on.
- Reproduction: Even though roots are not the regenerative piece of plants, they are vegetative parts. In certain plants, the roots are a method for proliferation. For example, new plants emerge from crawling-level stems called sprinters (stolons) in jasmine, grass, and so forth. This kind of multiplication is called the vegetative spread.
- Ecological Function: They actually look at soil disintegration, and give food, and furthermore territory to different organic entities.
What is a height of a tree?
The height of a tree is the total number of edges from a leaf node to any particular node usually a root node.
The height of a tree at the leaf node is minimum at (height of node F = 0) and maximum at the root node (Height of node A = 2).
Example of the Height of a tree
Shade avoidance response
Structure of Roots
Root Cap
The root is covered at the tip by a thimble-like design. This is known as called a root cap. The root cap protects the delicate root zenith when it clears its path through the dirt.
Region of Meristematic Activity
This area is also known as the region of cell division. This area lies a couple of millimeters over the root cap. This is the district of meristematic action. The cells in this district are tiny and have a slender divider and thick cellular material. Since this is the meristematic area, the cells partition quickly.

Region of Elongation
This area lies over the locale of the meristematic movement. The cells close to this district go through quick extension and growth. These cells are answerable for the development of roots long.
Region of Maturation
This area is simply over the locale of the extension. The cells from the locale of extension separate and mature, and afterward structure the district of development. The root hairs turn out around here. Root hairs are essential for the root epidermis.
Javascript
let N = 7, Root = 1;
addEdge(1, 2, adj);
addEdge(1, 3, adj);
addEdge(1, 4, adj);
addEdge(2, 5, adj);
addEdge(2, 6, adj);
addEdge(4, 7, adj);
function printParents(node, arr, parent)
if (parent == 0)
if (cur != parent)
printParents(cur, arr, node);
function printChildren(Root, arr)
let vis = new Array(arr.length).fill(0);
let node = q.shift();
console.log(cur + " ");
function printLeafNodes(Root, arr)
for (let i = 1; i < arr.length; i++)
console.log(i + " ");
if (i == Root)
console.log("The parents of each node are:");
printParents(Root, adj, 0);
console.log("The children of each node are:");
console.log("The leaf nodes of the tree are:");
console.log("The degrees of each node are:");
The parents of each node are: 1->Root 2->1 5->2 6->2 3->1 4->1 7->4 The children of each node are: 1-> 2 3 4 2-> 5 6 3-> 4-> 7 5-> 6-> 7-> The leaf nodes of the tree are: 3 5 6 7 The degrees of each node are: 1: 3 2: 2 3: 0 4: 1 5: 0 6: 0 7: 0
Root system architecture (RSA)
Terms and components
Extrinsic factors affecting root architecture include gravity, light exposure, water and oxygen, as well as the availability or lack of nitrogen, phosphorus, sulphur, aluminium and sodium chloride. The main hormones (intrinsic stimuli) and respective pathways responsible for root architecture development include:
What is a child node?
Or we can also say that every node excluding the root node is a child node in the tree. A child node always has a parent node to which it is connected. As you can see in the example below.
- Where nodes (B) and (C) are children of the node (A).
- Similarly, node (D) and node (E) are child nodes of (B).
- And node (F) and node (G) are child nodes of (C).
Child node in a tree.
Python3
def printParents(node, adj, parent):
if (parent == 0):
print(node, "->", parent)
if (cur != parent):
printParents(cur, adj, node)
def printChildren(Root, adj):
while (len(q) > 0):
print(node, "-> ", end=" ")
print(cur, " ", end=" ")
def printLeafNodes(Root, adj):
for i in range(0, len(adj)):
print(i, end=" ")
def printDegrees(Root, adj):
for i in range(1, len(adj)):
print(i, ": ", end=" ")
if (i == Root):
Root = 1
for i in range(0, N+1):
print("The parents of each node are:")
printParents(Root, adj, 0)
print("The children of each node are:")
print("The leaf nodes of the tree are:")
print("The degrees of each node are:")
What is a root node?
A node that is the first or topmost node in a tree is called a root node. In every tree, there is always one root node, which is the only node that has never previously been connected to another node.
The root node in this tree is node (A).
Characteristics of Root
- Chlorophyll is not present in roots, and because of that, they are not green in color.
- They don’t have nodes and internodes.
- Root hair is present on the roots, which helps in the absorption of nutrients.
- Root shows different types of movements
- Positive Geotrophism-Growth of roots towards gravity.
- Positive Hydrotropism-Growth towards the water.
- Negative Phototropism-Movement of roots away from sunlight.
- Roots are protected via root caps at the tips of the root.
The actual tip of the root is covered by a thimble-formed root cap, which protects the developing tip as it clears its path through the dirt. Apical meristem is present directly under the root cap, a tissue of effectively partitioning cells. A portion of the cells created by the apical meristem are added to the root cap, yet the majority of them are added to the area of extension, which lies simply over the meristematic district.
Application of Tree Data Structure
- File System: This allows for efficient navigation and organization of files.
- Data Compression: Huffman coding is a popular technique for data compression that involves constructing a binary tree where the leaves represent characters and their frequency of occurrence. The resulting tree is used to encode the data in a way that minimizes the amount of storage required.
- Compiler Design: In compiler design, a syntax tree is used to represent the structure of a program.
- Database Indexing: B-trees and other tree structures are used in database indexing to efficiently search for and retrieve data.
static void AddEdge(int x, int y, List<List<int> > adj)
static void PrintParents(int node, List<List<int> > adj,
if (parent == 0)
Console.WriteLine(node + "->Root");
Console.WriteLine(node + "->" + parent);
PrintParents(cur, adj, node);
static void PrintChildren(int root,
List<List<int> > adj)
var q = new Queue<int>();
int node = q.Dequeue();
Console.Write(node + "-> ");
Console.Write(cur + " ");
static void PrintLeafNodes(int root,
List<List<int> > adj)
for (int i = 1; i < adj.Count; i++)
Console.Write(i + " ");
static void PrintDegrees(int root, List<List<int> > adj)
Console.Write(i + ": ");
if (i == root)
int n = 7, root = 1;
var adj = new List<List<int> >();
for (int i = 0; i <= n; i++)
Process summary
1. First, create the necessary directories required by the root file system. You can refer to the root directory of the Linux system.
2. Then you need to create device nodes for the necessary devices. The init process needs to use the two device files /dev/console and /dev/null.Call mdev to build dev according to system requirements. (Automatically create device files)
3. If necessary, create a symbolic link.
4. If the file system is used with other platforms, a cross compiler is required. Copy the library files of the cross compiler to the corresponding root file system.
5. Then create various scripts and configuration files in the etc directory. For example: inittab file (system startup script), rcS script, network card startup script, profile file, port number file protocols, passwd file, etc.
6. Porting related tools: busybox dropbear (lightweight sshd server,openSSHsmall)
Related operations in etc directory
1. Create the /etc/inittab file
inittabThe configuration file used by the init initialization program when initializing the file system for Linux. This file is responsible for setting the init initialization program where the initialization script is; the commands to be run during the initialization of each run level; the commands corresponding to startup, shutdown, and restart; the commands to run when each run level is logged in.
# mount all the file systems specified in /etc/fstab (fstab will be created next) -a#Use mdev as hotplug to auto mount USB storage or SD card (mdev for device hotplug management) /sbin/mdev > #Use mdev to auto generate the device node in /dev path#mdev dynamically sorts out the registered devices through the proc and sys file systems, and then generates their corresponding nodes under /dev/, -s#make shm, pts support -p /dev/pts -p /dev/shm#pts is the remote virtual terminal. devpts is the remote virtual terminal file device. You can understand the basic situation of the current remote virtual terminal through /dev/pts. (Devpts, like proc, is a virtual file system) -t devpts devpts /dev/pts#Mount our apps/info partition -o sync,noatime,ro -t jffs2 /dev/mtdblock6 /apps -o sync,noatime,ro -t jffs2 /dev/mtdblock7 /info#Set hostname (-F means file, read hostname from file) - /etc/hostname#Enable console logon (Set terminal information) - ttyS vt10# now run any rc scripts (Execute rcS first).d/rcS# system daemon#Syslogd The process of recording application or device logs -n -n# Stuff to do before rebooting (reboot) /apps /info klogd syslogd -a -r- initdefault: This configuration item specifies the default run level of the system.
- respawn: If the process specified by the configuration item is ended, the process is restarted.
- wait: Do not execute the next configuration item before the process specified by the configuration item ends。
- once: After switching to the corresponding run level, execute the specified process only once.
- sysinit: No matter what run level is started, the process specified by this configuration item will be executed when the system starts.
- boot: Execute only once when the system starts.
- bootwait: Execute only once when the system starts, do not execute the next configuration item before the end of execution
- powerfail: Execute the process specified by this item when receiving a power failure notification from UPS.
- powerwait: Same as powerfail, but init will wait for the process to finish.
- powerokwait: Executed when a power supply notification from UPS is received.
- ctrlaltdel: Execute the process specified by this item when the user presses Ctrl+Alt+Del at the same time.
2. Create etc/init.d/rcS script
#function: In the /etc/init.d/ directory, any file that starts with an uppercase S will be executed, so if you want to write a script to automatically start at boot, you can put it in this directory and put File names start with capital S i /etc/init.d/S??* ; 3. Configure the network card self-start script:
ifconfig eth0 . netmask . upBecause the modified script is placed in the init.d directory, the opened opportunity can be started automatically.
4. Create a startup script that supports the /apps/etc directory
(test /apps/etc/init.d) ##If it is a directory i /apps/etc/init.d/S??* ; 5. Modify all file permissions in the init.d directory
[[email protected] etc]$ chmod 777 init.d/*
[[email protected] etc]$ ll init.d/
total 12
-rwxrwxrwx trainning rcS-rwxrwxrwx trainning -rwxrwxrwx trainning 6. Create fstab file
#devpts /dev/pts devpts defaults 0 0#/dev/root / ext2 rw,noauto 0 1 / defaults /tmp tmpfs defaults /dev tmpfs defaults /sys sysfs defaults 7. Create hostname, hosts, TZ files
[yangni etc]echo > hostname
[yangni etc]echo "127.0.0.1 yangni" >> hosts #Local ip and hostname[yangni etc]echo >>
[yangni etc]echo >> issue # Prompt message when system loginNote:
hosts file:
#File format: IPaddress hostname aliases File function: Provide the correspondence relationship between host name and IP address. It is recommended to change the host that you use frequently Add to this file, you can also add machines without DNS records to this file, which will facilitate network applications The system defaults to the following two, it is recommended to keep: localhost localhost localhost4 localhost44
:: localhost localhost localhost6 localhost66 The newly added must have three fields: {IP, FQDN (fully qualified domain name/full name domain name), HOSTNAME}
jx jx8. Create a profile file
# /etc/profile: system-wide .profile file for the Bourne shells. PATH=\
/bin:\
/sbin:\
/usr/bin:\
/usr/sbin:\
/usr/local/bin:\
/apps/bin:\
/apps/tools:\
/apps/tslib/bin\# If running interactively, then: [ ]; [ ]; PS1= #ls command color settings alias ll='/bin/ls --color=tty -laFh' alias ls='/bin/ls --color=tty -F'#Terminal color settings LS_COLORS=; [ ]; PS1= PS1= # System Setting -o vi alias ll= USER=`id -un` LOGNAME= HOSTNAME=`/bin/hostname` HISTSIZE= #History shows the maximum number HISTFILESIZE= PAGER= EDITOR= INPUTRC=/etc/inputrc #File handles keyboard mapping for a specific situation, this file is used by Readline as the startup file #Debug is used to output information DMALLOC_OPTIONS=debug=x34f47d83,inter=,log=logfile VAR1= VAR2= VAR3= VAR4= VAR5= LD_LIBRARY_PATH=/lib:/usr/lib/ #Link library address# QT Extendded 4.4.3 Setting QTDIR=/apps/qt-extended-. QWS_MOUSE_PROTO= QWS_DISPLAY= QWS_DISPLAY= QWS_SIZE= QT_PLUGIN_PATH=/plugins/ QT_QWS_FONTDIR=/lib/fonts PATH=/bin: LD_LIBRARY_PATH=:/lib# Touch Scree tslib Setting TSLIB_ROOT=/apps/tslib TSLIB_CONFFILE=/etc/ts.conf TSLIB_CALIBFILE=/etc/pointercal TSLIB_TSDEVICE=/dev/event0 TSLIB_CONSOLEDEVICE=none TSLIB_FBDEVICE=/dev/fb0
;Some reference documents about environment variables:
1. Terminal color: referenceTerminal color settings
2. PS1 variables:
PS1=# \d: represents the date, the format is Weekday Month Date, such as "Mon Aug 1"# \H: The complete host name. For example, the training machine of Brother Bird is linux.dmtsai.tw, then the host name is linux.dmtsai.tw# \h: Take only the first name of the host name. In terms of the above, it is just linux, .dmtsai.tw is omitted.# \t: Display time, in 24-hour format, such as: HH:MM:SS# \T: Display time, 12-hour time format!# \A :Display time, 24-hour format, HH:MM# \v :BASH version information;# \w: The full working directory name. The home directory will be replaced with ~;# \W: Use basename to get the name of the working directory, so only the last directory name will be listed.# \#: Which command was issued.# \$: Prompt character, if it is root, the prompt character is #3. tslib is an open source program that can provide functions such as filtering, debounce, calibration and other functions for the samples obtained by the touch screen driver. It is usually used as the adaptation layer of the touch screen driver and provides a unified interface for the upper application.
9. Create a port number file protocols used by some protocols
This file is a network protocol definition file, which records all the protocol types of the TCP/IP protocol suite. Each line in the file corresponds to a protocol type, which has 3 fields, separated by TAB or spaces, respectively representing «protocol name», «protocol number» and «protocol alias».
# $Id: protocols,v 1.1.1.1 2001/09/12 19:03:24 andersee Exp $# Internet (IP) protocols# Updated for NetBSD based on RFC 1340, Assigned Numbers (July 1992).ip IP # internet protocol, pseudo protocol numbericmp ICMP # internet control message protocoligmp IGMP # Internet Group Managementggp GGP # gateway-gateway protocolipencap IP-ENCAP # IP encapsulated in IP (officially ``IP'') # ST datagram modetcp TCP # transmission control protocolegp EGP # exterior gateway protocolpup PUP # PARC universal packet protocoludp UDP
hmp HMP # host monitoring protocolxns-idp XNS-IDP # Xerox NS IDPrdp RDP # "reliable datagram" protocoliso-tp4 ISO-TP4 # ISO Transport Protocol class 4xtp XTP # Xpress Tranfer Protocolddp DDP # Datagram Delivery Protocolidpr-cmtp IDPR-CMTP # IDPR Control Message Transportrspf RSPF #Radio Shortest Path First.vmtp VMTP # Versatile Message Transportospf OSPFIGP # Open Shortest Path First IGPipip IPIP # Yet Another IP encapsulationencap ENCAP # Yet Another IP encapsulation10. Create mdev.conf file
The mdev command will find the mdev configuration file in the /etc directory: mdev.conf. If the file does not exist, when the mdev -s command is executed, it will prompt that mdev.conf cannot be found. At this time, we can create an empty mdev.conf file to solve this problem. Next, create the configuration /etc/mdev.conf to automatically mount the u disk and SD card using mdev
sd[][] 0:0 0777 @(mount /dev/$MDEV /mnt/usb)
sd[a-z] 0:0 0777 $(umount /mnt/usb)
ub[][] 0:0 0777 @(mount /dev/$MDEV /mnt/usb)
ub[a-z] 0:0 0777 $(umount /mnt/usb)
mmcblk[0-9]p[0-9] 0:0 0777 @(mount /dev/$MDEV /mnt/sdc)
mmcblk[0-9] 0:0 0777 $(umount /mnt/sdc)11. Create user group group file
groupname : password : gid : members
- The first field is the user group name
- The second field is the user group password. When it is x, the password is mapped to /etc/gshadow, which is non-reverse
- The third field is GID,Group number, Is a positive integer or 0, 0** is paid to the root user group; The system usually reserves some higher GIDs for virtual users of the system. Each system reserves different GIDs. Fedora reserves 500.So when we add a new user group, we start from 500**. The range of GID is determined by GID_MIN and GID_MAX in /etc/login.defs
- The fourth field is a list of users. Each user is separated by a comma. The password here represents the group password, which is rarely used. It allows users who are not in this group to temporarily inherit the permissions of the group through the newgrp command, and a new shell will be opened when the newgrp command is used. The password encryption method is the same as the password in the passwd file, so if you need to set a group password, use the passwd program to dummy a user, and then copy the encrypted password in the user’s password section to the /etc/group file. The members column represents the members of the group. We can add the users who need to join the group separated by commas. Members of the same group can inherit the permissions owned by the group.
12. Create a user passwd file:
- The first field is the login name
- The second field is the password, which is generally mapped to the shadow file
- The third field is UID (user id)
- The fourth field is GID (group id)
- The fifth field is the full name of the user. Gecos is the abbreviation of General Electronic Computer Operating System, which is a mainframe computer in Bell Labs.
- The sixth field is the user root directory
- The seventh field is the type of SHELL used by the user
13. Create a password mapping shadow file
root:(/wl51kMw4e/:::::::)
Shows the encrypted string password user root. new all authentication tokens updated successfully.
[yangni etc]cat /etc/shadow | grep root
/wl51kMw4e/- The first field: user name (also called login name), in /etc/shadow, the user name and /etc/passwd are the same, so that the passwd and the user record used in shadow are linked together; this field is not empty;
- The second field: password (encrypted), this field is non-empty;
- The third field: the time when the password was last modified; this time is the time interval (number of days) from January 1, 1970 to the last password modification. You can modify the user’s password through passwd and then check /etc/ Changes in this field in shadow;
- The fourth field: the minimum number of days between password changes; if the value of this field is empty, the account is permanently available;
- Fifth field: the maximum number of days between password changes; if the value of this field is empty, the account is permanently available;
- The sixth field: how many days in advance to warn the user that the password will expire; if the value of this field is empty, the account is permanently available;
- The seventh field: how many days after the password expires to disable this user; if the value of this field is empty, the account is permanently available;
- The eighth field: user expiration date; this field specifies the number of days the user is invalidated (the number of days starting from January 1, 1970), if the value of this field is empty, the account is permanently available;
The ninth field: reserved field, currently empty for future development;
:::Basic Terminologies In Tree Data Structure
- Parent Node: The node which is a predecessor of a node is called the parent node of that node. {B} is the parent node of {D, E}.
- Child Node: The node which is the immediate successor of a node is called the child node of that node. Examples: {D, E} are the child nodes of {B}.
- Root Node: The topmost node of a tree or the node which does not have any parent node is called the root node. {A} is the root node of the tree. A non-empty tree must contain exactly one root node and exactly one path from the root to all other nodes of the tree.
- Leaf Node or External Node: The nodes which do not have any child nodes are called leaf nodes. {K, L, M, N, O, P} are the leaf nodes of the tree.
- Ancestor of a Node: Any predecessor nodes on the path of the root to that node are called Ancestors of that node. {A,B} are the ancestor nodes of the node {E}
- Descendant: Any successor node on the path from the leaf node to that node. {E,I} are the descendants of the node {B}.
- Sibling: Children of the same parent node are called siblings. {D,E} are called siblings.
- Level of a node: The count of edges on the path from the root node to that node. The root node has level 0.
- Internal node: A node with at least one child is called Internal Node.
- Neighbour of a Node: Parent or child nodes of that node are called neighbors of that node.
- Subtree: Any node of the tree along with its descendant.
Java
public static void
printParents(int node, Vector<Vector<Integer> > adj,
if (parent == 0)
System.out.println(node + "->Root");
System.out.println(node + "->" + parent);
for (int i = 0; i < adj.get(node).size(); i++)
if (adj.get(node).get(i) != parent)
public static void
printChildren(int Root, Vector<Vector<Integer> > adj)
Queue<Integer> q = new LinkedList<>();
int node = q.peek();
System.out.print(node + "-> ");
+ " ");
public static void
printLeafNodes(int Root, Vector<Vector<Integer> > adj)
for (int i = 1; i < adj.size(); i++)
if (adj.get(i).size() == 1 && i != Root)
System.out.print(i + " ");
public static void
printDegrees(int Root, Vector<Vector<Integer> > adj)
System.out.print(i + ": ");
if (i == Root)
System.out.println(adj.get(i).size() - 1);
int N = 7, Root = 1;
Vector<Vector<Integer> > adj
= new Vector<Vector<Integer> >();
System.out.println("The parents of each node are:");
printParents(Root, adj, 0);
"The children of each node are:");
"The leaf nodes of the tree are:");
System.out.println("The degrees of each node are:");
What is root?
Roots are a crucial part of all vascular plants. Roots help the plant to interact with the soil and help the plant to get the essential nutrients, water, and vitamins from the soil. Roots help to get water from the soil which is very important for proper growth and photosynthesis. Different types of modification of roots are seen according to the requirements. Not all plants have roots under the ground some have roots over the surface such roots are known as aerial roots. Aerial roots also provide nutrients, water, vitamins, and anchor the plant to a wall or rock.
Various other particular roots exist among vascular plants. Pneumatophores, generally found in mangrove species that fill in saline mud pads, are horizontal roots that develop vertically out of the mud and water to work as the site of oxygen admission for the lowered essential underground root growth. The underlying foundations of specific parasitic plants are exceptionally adjusted into haustoria, which implant into the vascular arrangement of the host plant to take care of the parasite.

Importance of root node
- The root node, which has no parents, is the highest node in the tree structure.
- The entire message is represented by this node, which is a global element.
- It may have one or more child nodes, but it is never recurring or able to have sibling nodes.
- You can change the root node’s name.
Modification of Root
Modification for Food capacity
Tap underlying foundations of turnip and carrot and unusual underlying foundations of yam are instances of alteration of root for food capacity.
Modification for Support
In banyan trees, hanging uncovers come from branches. The hanging roots then go into the dirt to offer extra help to the gigantic banyan tree. Such roots are called prop roots. If there should be an occurrence of a maize plant, uncovers rise up out of the lower hub of the stem and go into the ground. Such roots are called brace roots and offer extra help.
Modified for Respiratory
In plants that fill in swamps, many roots come out upward over the ground. These are empty roots are called pneumatophores. They work with the trade of gases in the roots. Due to waterlogging in swamps, it is beyond the realm of possibilities for roots to inhale air. Pneumatophores make up for this deficiency and permit the trade of gases. Rhizophora is a tree of mangrove timberland, which shows the presence of pneumatophores.
FAQs on Root
Question 1: What are the various kinds of root morphology?
Based on the beginning the roots can be characterized by the accompanying sorts
- Taproot: (Example: Dicots-Mustard) Thick essential root emerges straightforwardly from the radicle and develops inside the dirt.
- Fibrous root: (Example: Monocots-Wheat)
- Adventitious or unusual roots: (Example: Grass, Monstera, Banyan tree)
Question 2: What are the Characteristics of roots?
Characteristics of roots are:
- The root is the plummeting part of the plant hub.
- It is emphatically geotropic.
- It is normally non-green or brown in variety.
- The root isn’t additionally separated into hubs and internodes
Question 3: What are root hairs?
The thin extensions from the epidermal cell are called epiblema. Such thin hairs are known as root hairs
Question 4: Which mechanism roots uses for the uptake of nutrients?
Roots absorb nutrients or uptake water via diffusion, facilitated diffusion, and active transport.
Question 5: What is the distinction between taproot and fibrous root?
Taproot enters profound into the dirt, while a stringy root is shallow and doesn’t infiltrate as profoundly. A taproot is the separated essential foundation of the plant, while the stringy root isn’t the separated essential base of the plant.
Five, copy the dynamic library in the cross compiler to the corresponding directory
[yanngi rootfs] -af /opt/buildroot-/arm920t/usr/arm-unknown-linux-uclibcgnueabi/sysroot/lib/* lib/
[yanngi rootfs] -af /opt/buildroot-/arm920t/usr/arm-unknown-linux-uclibcgnueabi/lib/* lib/The appeal step can be done with a security script:
[ != ] ; ;
INST_PATH= [ ! -o == ] ; " is not exist or it's root path,exit now" ; [ ! /data ] ; "It's not an embedded root file system tree" ;
CROSSTOOL_PATH=/opt/buildroot-/arm920t/usr/
CMD_PREFIX= -ev
LIB_PATH=/lib
USR_LIB_PATH=/usr/lib rm -rf /*.so* rm -rf /* cp -af /arm-unknown-linux-uclibcgnueabi/sysroot/lib/*.so* cp -af /arm-unknown-linux-uclibcgnueabi/lib/*.so* cp -af /lib/*.so* #$CMD_PREFIX sudo rm -rf $LIB_PATH/libmudflap* rm -rf /libstdc++.so..-gdb.py
mkdir -p lib cp -af /arm-unknown-linux-uclibcgnueabi/sysroot/usr/lib/*.so* lib#$CMD_PREFIX cp -af $CROSSTOOL_PATH/arm-unknown-linux-uclibcgnueabi/sysroot/usr/lib/engines lib rm -rf lib/libstdc++.so* mv lib/*
rm -rf libTwo, create a directory
├── apps #Mount the directory for the partition where the Application is located├── bin
├── data
├── dev
├── etc
│?? ├── dropbear #dropbear ssh server dependent files│?? └── init.d #System startup initialization script ├── info
├──
│?? └── modules #insmod depends on the /lib/modules/kernel version directory│?? └──
├── mnt #Some mount points of the device at runtime│?? ├── dev
│?? ├── nfs
│?? ├── sdc
│?? └── usb
├── proc
├── root
├── sbin
├── sys
├── tmp
├── usr
│?? ├── bin
│?? ├──
│?? ├── sbin
│?? └── share
└── var3. Create a device file in the Dev directory
Because after the kernel mounts the file system, the init process needs to use the two device files /dev/console and /dev/null to call mdev to build dev, so these two device files must be created statically when making the file system, otherwise Will prompt when the system starts
Waring:unable to open an initial console:
-m means authority major: major device number minor: minor device
[yangni rootfs]sudo mknod -m666 dev/null c
[yangni rootfs]sudo mknod -m666 dev/console c
[yangni rootfs]sudo mknod -m666 dev/ttyS c
[yangni rootfs]sudo mknod -m666 dev/ttySAC c
[yangni rootfs]sudo mknod dev/mtdblock b
[yangni rootfs]sudo mknod dev/mtdblock1 b
[yangni rootfs]sudo mknod dev/mtdblock2 b
[yangni rootfs]sudo mknod dev/mtdblock3 b
[yangni rootfs]sudo mknod dev/mtdblock4 b
[yangni rootfs]sudo mknod dev/mtdblock5 b
[yangni rootfs]sudo mknod dev/mtdblock6 b
[yangni rootfs]sudo mknod dev/mtdblock7 b
[yangni rootfs]sudo mknod dev/mtdblock8 b
[yangni rootfs]sudo mknod dev/mtdblock9 b
[yangni rootfs]ls -l dev/
total
crw-rw-rw- root root , console
brw-r--r-- root root , mtdblock
brw-r--r-- root root , mtdblock1
brw-r--r-- root root , mtdblock2
brw-r--r-- root root , mtdblock3
brw-r--r-- root root , mtdblock4
brw-r--r-- root root , mtdblock5
brw-r--r-- root root , mtdblock6
brw-r--r-- root root , mtdblock7
brw-r--r-- root root , mtdblock8
brw-r--r-- root root , mtdblock9
crw-rw-rw- root root , null
crw-rw-rw- root root , ttyS
crw-rw-rw- root root , ttySACNeed for Tree Data Structure
1. One reason to use trees might be because you want to store information that naturally forms a hierarchy. For example, the file system on a computer:

2. Trees (with some ordering e.g., BST) provide moderate access/search (quicker than Linked List and slower than arrays).
3. Trees provide moderate insertion/deletion (quicker than Arrays and slower than Unordered Linked Lists).
4. Like Linked Lists and unlike Arrays, Trees don’t have an upper limit on the number of nodes as nodes are linked using pointers.
What is a parent node?
The node which is a predecessor of another node is known as a parent node.
Or we can also say that if a node (A) is connected to another node (B) then node (A) will be known as the parent node for node (B) and similarly for other nodes as well if you refer to the below example.
- Node (A) is the parent of node (B) and node (C).
- Similarly, node (B) is the parent of node (D) and node (E).
- And node (C) is the parent of node (F) and node (G).
Parent nodes in a tree.
Eight, transplant dropbear
Dropbear is a relatively small SSH server and client. dropbear implements the Secure Shell (SSH) protocol. Can be used to establish a remote connection.
1. First compile and generate the PC version, which is used when making the key
[yangni ~]wget /-..tar.bz2
[yangni ~]tar -xjf dropbear-..tar.bz2
[yangni ~]cd dropbear-.
[yangni dropbear-.]./configure && makeGenerated file:
dropbear: ssh2 server
dropbearkey: key generator
dropbearconvert: can convert openssh keys
dbclient: ssh2 client can be used to connect to remote servers
Scp can write and retrieve files to and from remote servers
rsa -f /opt/rootfs/etc/dropbear/dropbear_rsa_host_key
Will output bit rsa secret
Generating , this may a ... portion :
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAAAgwChXpm6ogojmWy7GTZloJDdSIFq7pd49P3dh2I8Ap/Cr9KRWlfQb0rchkFv1h62736FyX28S1jo7HpES9Rjp7MinG66pyzFjOfrsruzkeheo7YBrk8GPeSdEm65O3gPlJzReyMY3r020fwVIGaMf7+bPBuMsYY1g+OcgeEygYCExz [email protected]Fingerprint: md5 ed:a6:c9:d:e::f6::b2:c::::be:b: /opt/rootfs/etc/dropbear/dropbear_dss_host_key
Will output bit dss secret key
Generating key, this may a key portion is:
ssh AAAAB3NzaC1kc3MAAACBAOa5XsTcByi4cdnhJ44Uro/athrTzv68yeizFejzQMK1e4ung/SfAIZW/ms41HSSMhO6Siv/oOGz3cPnw8NKkWHWTP6pQmyZlvl2zNdrbDwiPGQ17rb5THoVDbXwn54c/aMR27mjDBJ4SDpL08wfs6k2JaelQIpBYWbFJrAAAAFQCgrFTR2dqbRdrklhaxnU7L8ADiQAAAIEAwUThj2irqMRCuItsKNhYKmydUAtAL47ysGBYMxKH36cLBovm19gaBTKsdBJbBs7j//xrFLPypAQmN3MukeSQvIUGQ0qzqPEcwtOdDtqOzi2
Fingerprint: md5 :f3:::b:a6:b:a5:cc::e5::c:::cd2. Compile the ARM version
dropbear: ELF - LSB executable, ARM, version (SYSV), dynamically linked (uses libs), stripped3. Create a startup script in the file system
/usr/sbin/dropbear
[[email protected] rootfs]$ chmod etc/init.d/S04_dropbear
[[email protected] rootfs]$ ls
apps bin data dev etc info lib linuxrc mnt proc root sbin sys tmp usr varIn this way, the root file directory tree is completed, and then add the corresponding file system to start.
What is a leaf node?
A node that does not have any child node is called a leaf node.
Sometimes in this case if there is a single node (A) present in the tree then that node is also called a leaf node because of no child node connected to it. There is nothing connected to a leaf node further which is the endmost node of a tree in a direction.
Leaf node in a tree.
Why Tree is considered a non-linear data structure?
The data in a tree are not stored in a sequential manner i.e., they are not stored linearly. Instead, they are arranged on multiple levels or we can say it is a hierarchical structure. For this reason, the tree is considered to be a non-linear data structure.